Our SSL/TLS engine accelerates and offloads processing for encryption / decryption and authentication in SSL / TLS by combining our TCP offload and crypt engine.
Since the record layer processing is completely hardware offloaded, the user application can overwhelmingly reduce the CPU load which only needs preparing the data to transfer securely.
In addition, by creating the SSL/TLS tunnel between the terminal and the host, the high performance and low latency VPN is possible.
Two types of IP are available, one for embedded devices and the other for servers.
HW takes over high-performance, low-latency secure communication and contributes to power consumption reduction
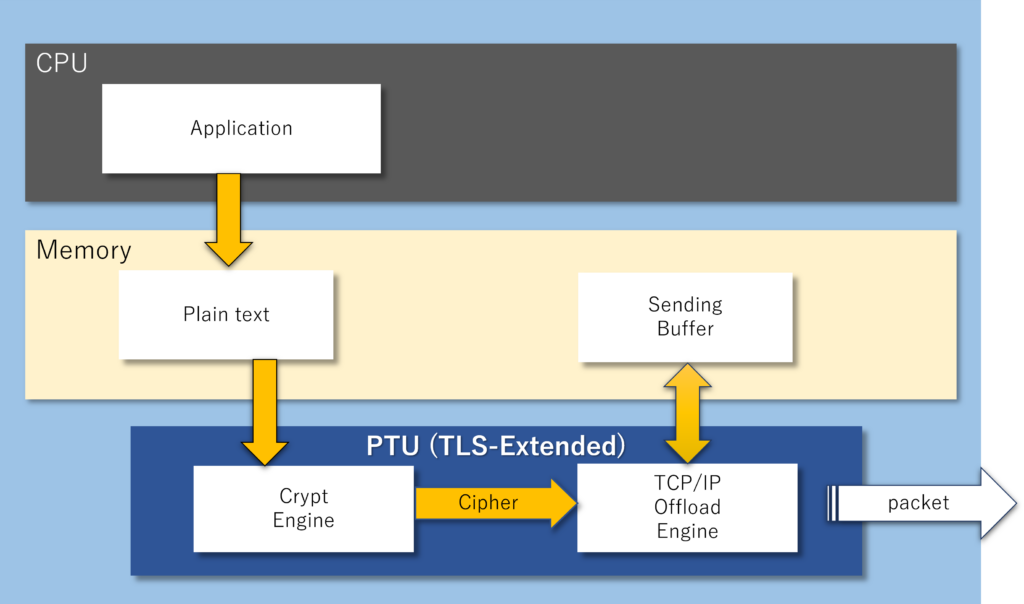
With PTU (TLS extension) integrated with the crypto engine, the data transmission process in SSL / TLS is completed with full hardware.
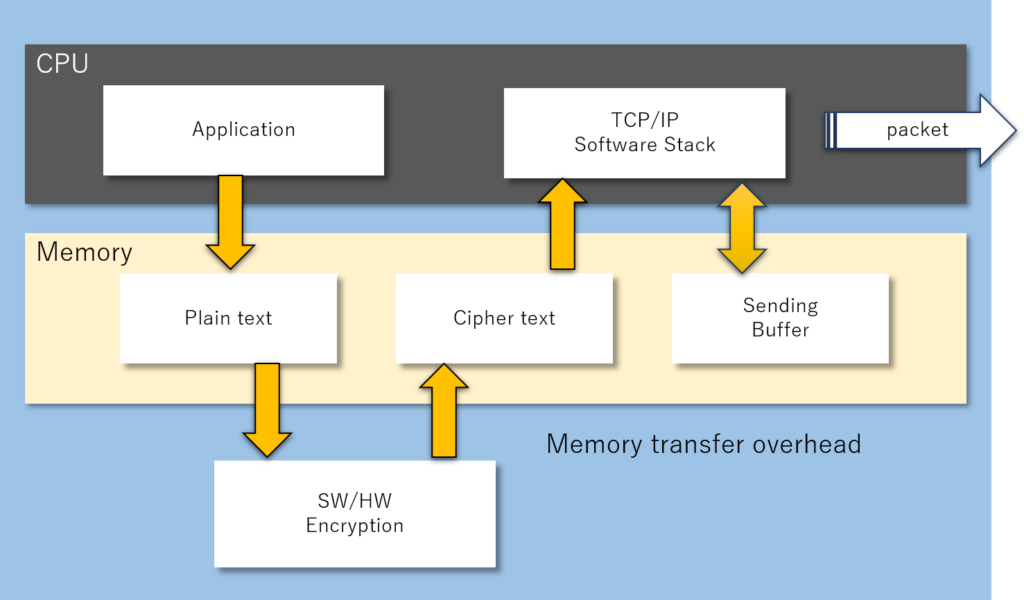
Even if a dedicated HW is used for encryption, memory transfer occurs before and after encryption in a normal system. This is because the TCP / IP protocol stack is separated (left figure).
However, with Intellectual Highway’s TLS-enhanced PTU, there is no extra memory transfer of encrypted data or data required for the TLS protocol (right figure). Therefore, high-performance, low-latency secure communication is achievable.
Applicable to any application
Our SSL/TLS accelerators are software-integrated and can be applied to any applications to speed up processing and reduce CPU load.
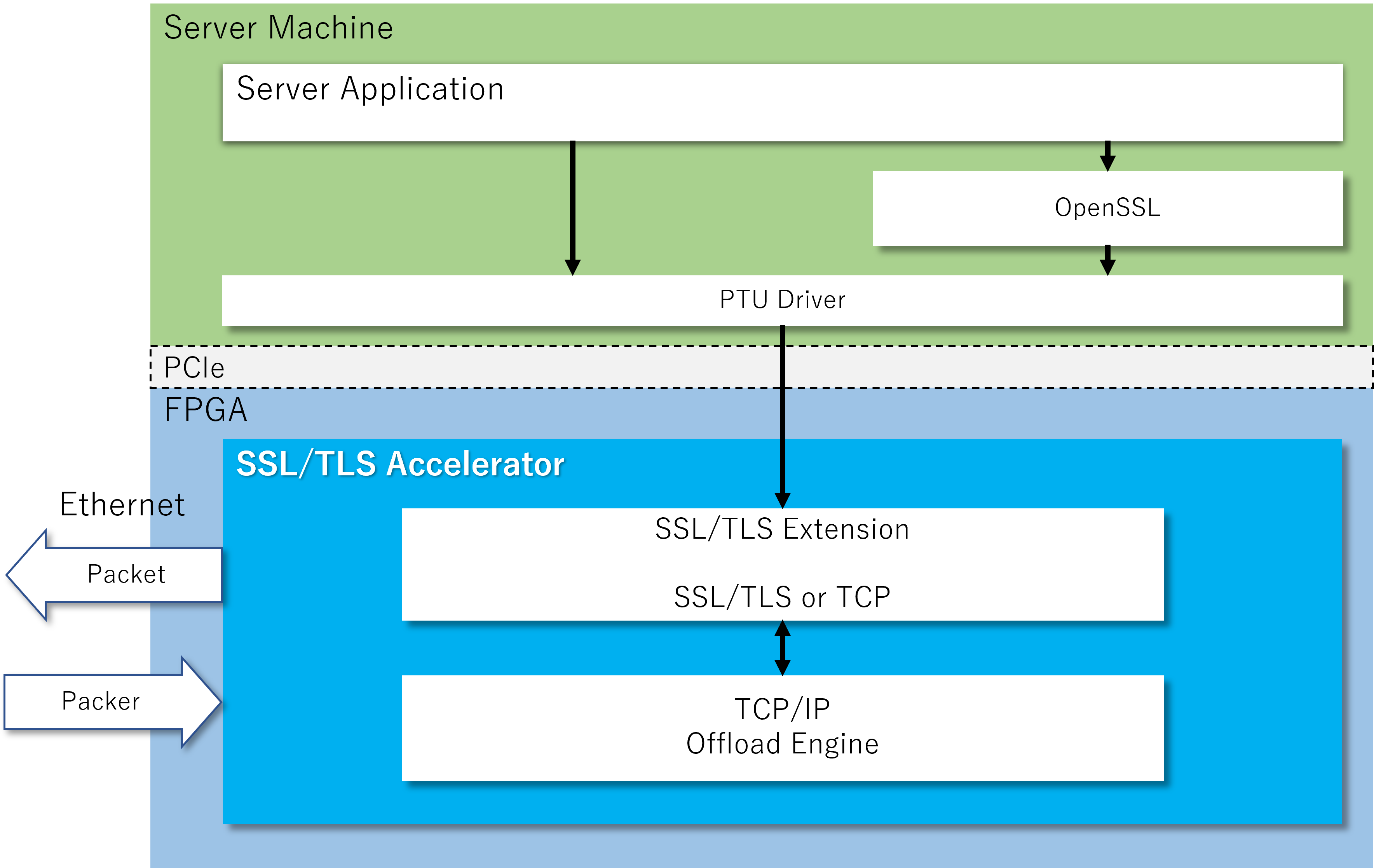
For example, if your service uses OpenSSL, simply adding on an FPGA card written with our SSL/TLS accelerator to the server machine will improve performance of the service and the CPU power can be dedicated to the application without changing user applications.
Use case1 : OpenSSL Accelerator
Accelerate server applications that use OpenSSL.
By using our PTU driver, this IP is used as the back-end of OpenSSL to send and receive SSL/TLS packets. The secure communication module and TCP offload engine performs all the layer processing below SSL/TLS in hardware, and packets are sent and received using Ethernet interface on the FPGA board.
In addtion, all protocols other than SSL/TLS are also supported by the PTU and can be sent and received via Ethernet on the FPGA board.
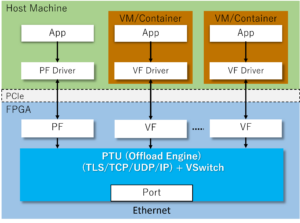
Our SSL/TLS offload engine supports SR-IOV (Single-Root I/O Virtualization), allowing multiple VMs and containers to use the full performance of the offload engine without software overhead. This allows for multi-tenant use, where multiple customers can use the same physical machine.

Use case2 : TLS Proxy (HTTPS Proxy)
As a Proxy server, HW ensures that plaintext communication (eg HTTP) on client machines to secure protocols (eg HTTPS). At the same time as reducing the load of HTTPS encryption processing on the client machine, communication to the outside is forced to be encrypted. Also, the security management can be easier because the inside of the intranet is in plain text.
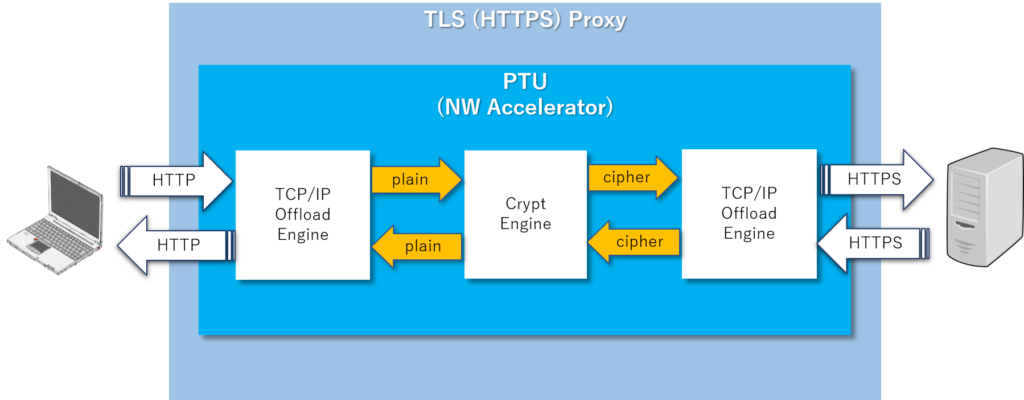
This is a demo that converts HTTP access from a client to HTTPS with PTU on FPGA and replaces communication between servers with TLS communication. In the captured log, TLS encapsulation can be seen.
Specification
| SSL/TLS | Protocol : TLS Record Protocol |
|---|---|
| Performance | Throughput: Maximum 50-100Gbps(depends on device and number of sessions) |
| Device | 100Gbps available device: N6010 etc (Altera Agilex) |

